The document RFC 8484 defines a specific protocol, DNS over HTTPS (DoH), for sending DNS queries and getting DNS responses over HTTP using https URIs (and therefore TLS security for integrity and confidentiality). This is an Internet Standards Track document, it represents the consensus of the IETF community. Some experts speak negatively about the IETF decision.
Hundreds of popular sites will be blocked in the new Chrome 70
New version of the browser Chrome 70, which is expected to be released on October 16, will block sites with certificates issued by Symantec, Thawte, VeriSign, Equifax, GeoTrust and RapidSSL before June 2016. Many popular resources are still not ready for this. According to security researcher Scott Helme 1139 sites in the top 1 million websites based on Alexa rankings will be affected.
Microsoft To-Do Integration in Skype and Outlook.com
In new Skype for Windows 10 update user will able to add, edit and check off tasks directly from app. Tasks will be saved and available in Skype, or in the To-Do app. You also will be able easily manage your tasks in Outlook.com without breaking your flow or leaving your inbox.
Microsoft released Office 2019 for Windows and Mac
The updated Office includes classic versions of Word, Excel, PowerPoint, Outlook, Publisher 2019, Access 2019, Project 2019 and Visio 2019. Office 2019 is compatible with Windows 10 and the three most recent versions of macOS. The list of new key features and answers to frequently asked questions published on Microsoft website.
Windows 10 October 2018 Update: removed or no longer developing features
Before the release of the new Windows 10 October 2018 Update (version 1809), Microsoft published the list of removed or planned for replacement features.
Removed features:
- Business Scanning, also called Distributed Scan Management (DSM);
- FontSmoothing setting in unattend.xml;
- Hologram app;
- limpet.exe;
- Phone Companion;
- Trusted Platform Module (TPM) management console;
- Future updates through Windows Embedded Developer Update for Windows Embedded Standard 8 and Windows Embedded 8 Standard.
No longer developing features:
- Companion device dynamic lock APIS;
- OneSync service;
- Snipping Tool.
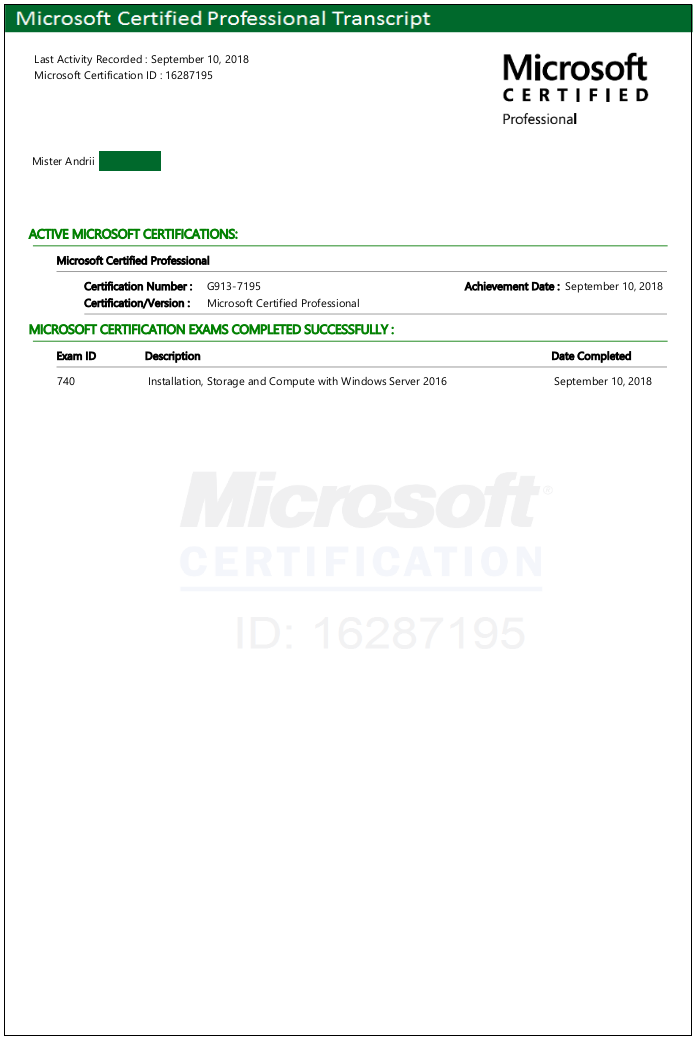
Microsoft Windows Server 2016 certification exam
Our specialists continue to confirm their qualifications: we congratulate our colleague Andrii on the successful passing of the 70-740 Installation, Storage and Compute with Windows Server 2016 exam. This exam tests the knowledge about installation, storage, and compute functionalities available in Windows Server 2016. Candidates perform general installation tasks, including installing and configuring Nano Server, as well as creating and managing images for deployment.
Our team certificates.
Google wants to display URLs without subdomains
Google wants to refuse displaying subdomains like «www» and «m» in URLs and make it simpler and more understandable for everyone. According to developers, subdomains and other elements in the URL only complicate web identity for ordinary users. Experts have already discovered errors in the work, give examples of incorrect transforms when stripping subdomains.
New features of the Outlook on the web
Microsoft announced some of the new features:
- search;
- files;
- suggested replies;
- simplified event creation;
- smart room suggestions;
- simplified add-in experience;
- more ways to use and manage groups in Outlook.
Simply click on the “Try the new Outlook” toggle on the top right corner of inbox.
Microsoft Windows 0-day vulnerability in the ALPC interface
Information about 0-day vulnerability was first disclosed in Twitter by independent security researcher. The CERT / CC specialist confirmed that Windows Task Scheduler contains a local privilege escalation vulnerability in the ALPC interface. Public exploit code works on 64-bit Windows 10 and Windows Server 2016 systems, and with minor modifications with 32-bit Windows 10. Security consultancy Acros Security released unofficial patch for the 64-bit version of Windows 10 on its 0patch platform.
Microsoft Teams now ready to replace Skype for Business
Microsoft announced that Teams is ready to become the primary client for Intelligent Communications in Office 365. Company added many new communications features to Teams and released resources, tools and guidance to help current Skype for Business Online customers with their upgrade.