It would be great if the process of securing a Windows 10 device can be reduced to a simple checklist. But the process of securing is much more complicated than that. The initial setup simply establishes a security baseline. When this configuration is complete, security needs continued vigilance and ongoing effort. A big part of…
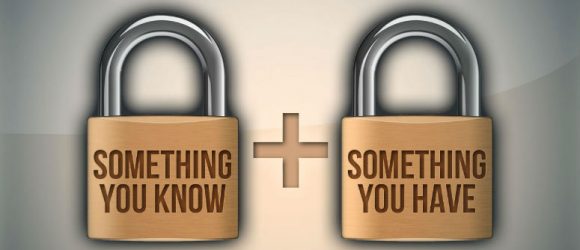
The competent approach to IT security in terms of server authorization, both inside and outside the company premises, implies a number of important measures. They include providing a unique user name and meeting password complexity requirements, as well as conducting the planned password change and non-disclosure of credentials to third parties, etc.