It would be great if the process of securing a Windows 10 device can be reduced to a simple checklist. But the process of securing is much more complicated than that. The initial setup simply establishes a security baseline. When this configuration is complete, security needs continued vigilance and ongoing effort. A big part of Windows 10 device security work happens remotely from the device.
The best security plan pays attention to network traffic, email accounts, authentication mechanisms, management servers, and other external connections. IT specialists should be able to carry out  these points. What about the small business without IT staff, outsourcing could be the best way.
these points. What about the small business without IT staff, outsourcing could be the best way.
The updates are being installed regularly and it is one of the most important settings for Windows 10 devices. Quality updates are delivered monthly through Windows Update. They address security and reliability issues and do not include new features. All quality updates are cumulative, so you no longer have to download dozens of updates after performing a clean install of Windows 10. You need install the latest update only and you will be completely up to date. Feature updates are the equivalent of what used to be called version upgrades. They include new features and require a multi-gigabyte download and a full setup.
When the updates are available on Microsoft’s update servers Windows 10 devices download and install them at once.
In the big companies, administrators can apply Windows Update for Business settings using Group Policy or mobile device management (MDM) software. You can also administer updates centrally by using a management tool such as System Center Configuration Manager or Windows Server Update Services.
User account management
Devices with Windows 10 edition (like Pro, Enterprise, or Education) can be joined to a Windows domain. It gives domain administrators an access to the Active Directory features and can authorize users, groups, and computers to access local and network resources. If you’re a domain administrator, you can manage Windows 10 PCs using the full set of server based Active Directory tools.
The smaller businesses have Windows 10 PCs that are not joined to a domain and they can choose of few account types: Local account on a Windows 10 PC is a member of the Administrators group and has the right to install software and modify the system configuration. Microsoft and Azure Active Directory (Azure AD) accounts should be set up as Standard users to prevent untrained users from inadvertently damaging the system or installing unwanted software. Windows Hello feature can be used for increasing the security of the sign-in process on your device. It requires a two-step verification process to enroll the device with a Microsoft account, an Active Directory account, an Azure AD account, or a third-party identity provider that supports FIDO version 2.0.

Then the user can sign in using a PIN or biometric authentication for example a fingerprint, facial recognition. The biometric data is stored on the device only and prevents a variety of common password-stealing attacks. On devices connected to business accounts, administrators can use Windows Hello for Business to specify PIN complexity requirements.
It is necessary to set-up multi-factor authentication (MFA) for protection Microsoft or Azure AD accounts on business PCs from external attacks. On Microsoft accounts, the Two-step Verification setting is available at link. For Office 365 Business and Enterprise accounts, an administrator must first enable the feature from the Office portal, after which users can manage MFA settings by going to link.
Data protection
No one can foresee theft of laptop or left behind it somewhere else, but such situations can lead to significant risk of data loss. Even worse if we are talking about regulated industries or where data breach laws require public disclosure. But there is an encryption tool that is available in business editions of Windows, called BitLocker. With BitLocker enabled, every bit of data on the device is encrypted using the XTS-AES standard. Using Group Policy settings or device management tools, you can increase the encryption strength from its default 128-bit setting to 256-bit. For full
 management capabilities, you’ll also need to set up BitLocker using an Active Directory account on a Windows domain or an Azure Active Directory account. In either configuration, the recovery key is saved in a location that is available to the domain or AAD administrator.
management capabilities, you’ll also need to set up BitLocker using an Active Directory account on a Windows domain or an Azure Active Directory account. In either configuration, the recovery key is saved in a location that is available to the domain or AAD administrator.
On an unmanaged device running a business edition of Windows 10, you can use a local account, but you’ll need to use the BitLocker Management tools to enable encryption on available drives. Also you should encrypt portable storage devices. USB flash drives. MicroSD cards used as expansion storage, and portable hard drives are easily lost, but the data can be protected from prying eyes with the use of BitLocker To Go, which uses a password to decrypt the drive’s contents.
Blocking malicious code
Nowadays, antivirus software is just another layer in protecting system, although time ago it wat the main tool for blocking the installation of malicious code.
Installation of Windows 10 includes Windows Defender. It is a built-in antimalware software. And it updates by its own, when the new updates are available on Windows Update. But if you decide to install another security package, Windows Defender allows that software to function. Large companies that use Windows Enterprise edition can deploy Windows Defender Advanced Threat Protection, a security platform that monitors endpoints such as Windows 10 PCs using behavioral sensors. Using cloud-based analytics, Windows Defender ATP can identify suspicious behavior and alert administrators to potential threats. For smaller businesses, the most important challenge is to prevent malicious code from reaching the PC in the first place. Microsoft’s SmartScreen technology is another built-in feature that scans downloads and blocks execution of those that are known to be malicious. The SmartScreen technology also blocks unrecognized programs but allows the user to override those settings if necessary.
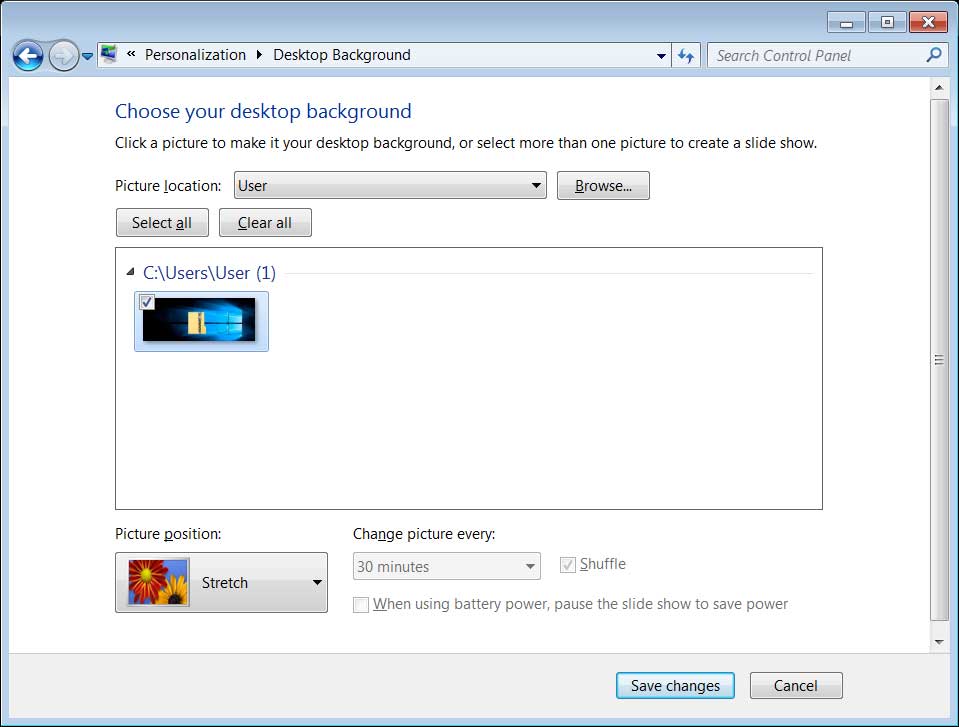
Another important step for protecting your PC is to be attentive to your mail. Cause infection PCs via attachment files in mails and links to malicious websites are common thing. Although email client software can offer some protection, blocking these threats at the server level is the most effective way to prevent attacks. An effective approach for preventing users from running unwanted programs (including malicious code) is to configure a Windows 10 PC from running any apps except those you specifically authorize. To adjust these settings on a single PC, go to Settings > Apps > Apps & Features; under the Installing Apps heading, choose Allow Apps From The Store Only. This setting allows previously installed apps to run, but prevents installation of any downloaded programs from outside the Microsoft Store.
Administrators can configure this setting over a network using Group Policy: Computer Configuration > Administrative Templates > Windows Components > Windows Defender SmartScreen > Explorer > Configure App install Control.
Networking
The Windows 10 firewall, supports three different network configurations: Domain, Private, and Public. Apps that need access to network resources can generally configure themselves as part of initial setup.
If you need to configurate basic Windows firewall settings, you should use the Firewall & Network Protection tab in the Windows Security app. «Advanced Settings» will lead you to expert-only set of configuration tools with Advanced Security console. These settings can be controlled through a combination of Group Policy and server-side settings.
The most complex problems with Windows 10 PC security appear when you connect to wireless networks. To increase the level of security in large organizations should add support for the 802.1x standard. It uses access controls instead of shared password. And when there is an attempt to connect to such type of network Windows 10 will reject unauthorized connections. On Windows domain-based networks, you can use the native DirectAccess feature to allow secure remote access.
Happens that it is important to connect to an untrusted wireless network. And the best way out is to configurate a virtual private network (VPN). To set up this type of connection, go to Settings > Network & Internet > VPN. Small businesses and individuals can choose from a variety of Windows-compatible third-party VPN services.






 In order to monitor server usage an admin should install the agent on the server. The management server receives this data from the agent and displays it to the user through the interface of the IT monitoring software, often in the form of a graph of performance over time.
In order to monitor server usage an admin should install the agent on the server. The management server receives this data from the agent and displays it to the user through the interface of the IT monitoring software, often in the form of a graph of performance over time.


 Managing updates using Group Policy
Managing updates using Group Policy Enterprise management tools
Enterprise management tools
 There are three variants of maintaining a Windows 7 install :
There are three variants of maintaining a Windows 7 install :
 these points. What about the small business without IT staff, outsourcing could be the best way.
these points. What about the small business without IT staff, outsourcing could be the best way.
 management capabilities, you’ll also need to set up BitLocker using an Active Directory account on a Windows domain or an Azure Active Directory account. In either configuration, the recovery key is saved in a location that is available to the domain or AAD administrator.
management capabilities, you’ll also need to set up BitLocker using an Active Directory account on a Windows domain or an Azure Active Directory account. In either configuration, the recovery key is saved in a location that is available to the domain or AAD administrator.